In the world of cybersecurity, we often focus on building taller walls and stronger locks. We use firewalls, antivirus, and complex EDR systems. But history has shown that a determined attacker will eventually find a way in. The real question is: How long will they be there before you notice? Introducing digital tripwires.
According to the official Canarytokens Guide, the answer lies in “digital tripwires.” Here is why and how you should be using Canarytokens to transform your security posture.
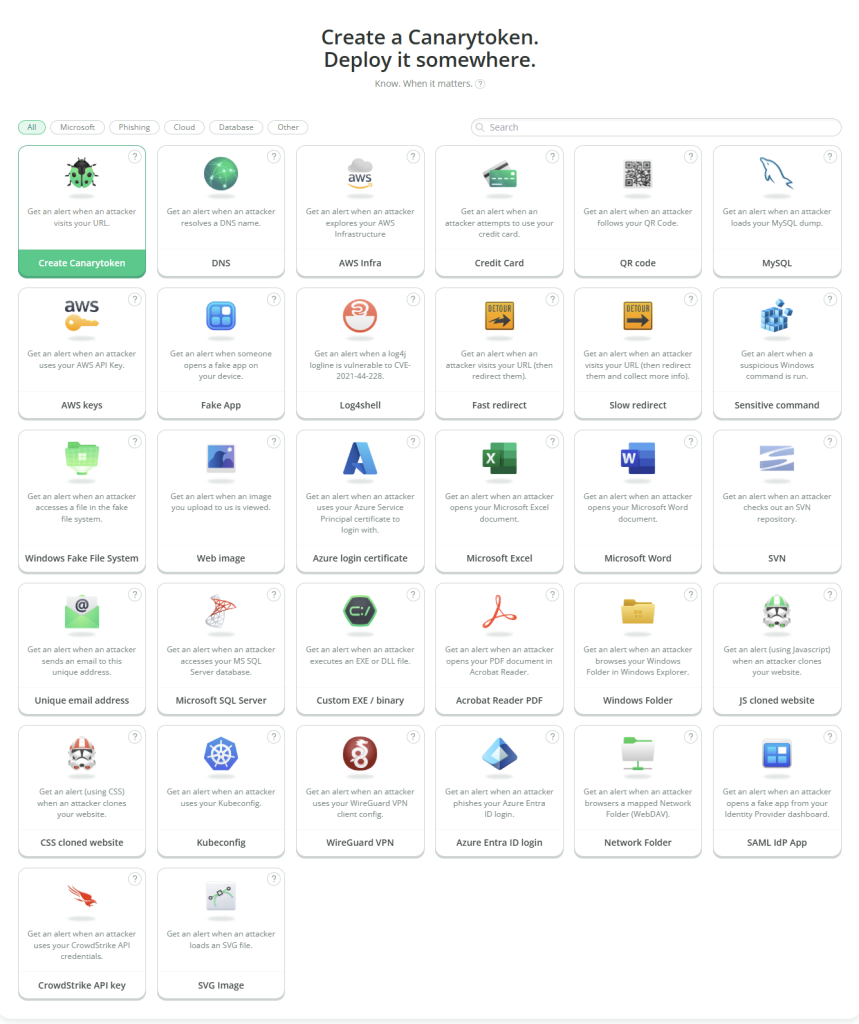
What is a Canarytoken?
Think of a Canarytoken as a silent motion sensor for your digital environment. It is a tiny “trap” – a file, a link, a credit card number, or an API key – that looks valuable to an attacker but serves no legitimate purpose for your employees.
Because nobody has a reason to touch these items, any interaction with them is a high-fidelity signal that something is wrong. When a token is “triggered” (e.g., a file is opened or a URL is visited), you get an instant alert with the IP address and metadata of the intruder.
Why Should You Use Them?
1. High Signal, Low Noise
One of the biggest problems in security is “alert fatigue.” Analysts are buried in thousands of logs daily. Canarytokens solve this because they never trigger a false positive if placed correctly. If your “Salary_Increases_2024.docx” file is opened, and you didn’t do it, you have a confirmed incident.
2. They Are “Set and Forget”
Unlike complex security software, Canarytokens are incredibly lightweight. They don’t require you to install agents on every laptop or run heavy background processes. You generate them, sprinkle them throughout your network, and forget about them until you get an email or a Slack notification.
3. Attackers Can’t Help Themselves
Attackers are looking for credentials, sensitive documents, and access keys. By placing a “juicy” looking token (like an AWS API key in a GitHub repo or a fake SQL database), you are essentially baiting the intruder into revealing their presence.
Spotlight: The Credit Card Canarytoken
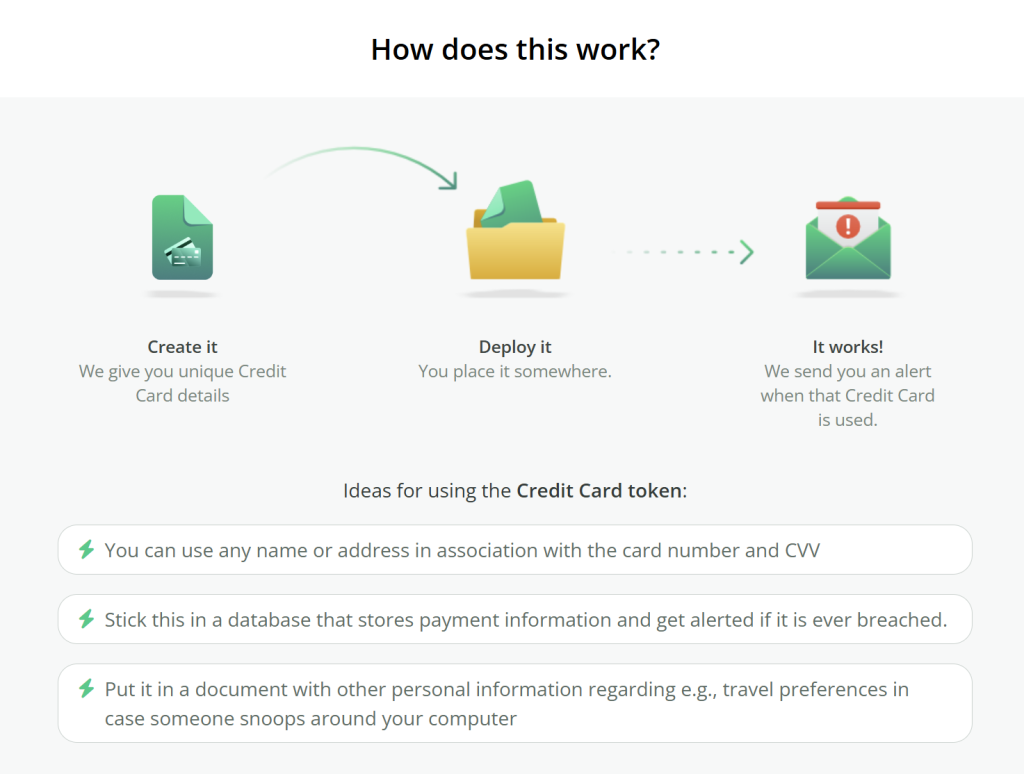
One of the most unique and effective tokens offered is the Credit Card Canarytoken.
Many attackers break into systems specifically to find financial data. With this token, you can generate a set of credit card details (Number, CVV, and Expiry) that look completely legitimate. You can store these in a database, a text file on a server, or even in your browser’s “autofill” history.
The magic happens when an attacker tries to “verify” or process the card. The moment they attempt to use these card details on any payment gateway or verification service, you receive an immediate alert. Since the card is fake and should never be used, any activity is a 100% guarantee that your data has been compromised.
How to Use Other Canarytokens: Top Strategies
The Canarytokens guide lists dozens of types, but here are some other effective ways to deploy them:
- MS Word/PDF Documents: Place a “confidential” document on a file share. If a hacker exfiltrates your data and opens the file later, the document will “phone home” and tell you where they are.
- AWS/Azure Keys: Create “dead” cloud credentials and place them in your source code or configuration files. If an attacker tries to use them to access your cloud, you’ll get an alert immediately.
- Cloned Websites: If you are worried about phishing, you can use a Cloned Website token. If someone copies your login page to steal credentials, you’ll be notified the moment their fake site goes live.
Conclusion
The goal of Canarytokens isn’t just to stop an attack, but to shrink the “dwell time”—the time an attacker spends in your network before being caught. By deploying these digital tripwires, you force the attacker to be right 100% of the time, while you only need them to make one mistake: touching the wrong file or trying to use the wrong credit card.
They are free, easy to deploy, and could be the difference between a minor incident and a catastrophic data breach.
Go and check out the webpage of the creator of Canary Tokens here: Thinkst Canary

